Every October when Cybersecurity Awareness Month arrives it can feel like a steady stream of reminders:
Update your devices.
Use better passwords.
Beware of suspicious links.
Those reminders are important, but they fail to capture everyday moments where security...
Every October when Cybersecurity Awareness Month arrives it can feel like a steady stream of reminders:
- Update your devices.
- Use better passwords.
- Beware of suspicious links.
Those reminders are important, but they fail to capture everyday moments where security matters the most. In my work as a security analyst, I have learned many tools to combat cyber threats. Parenting four daughters has taught me something entirely different: Practical safety grows from conversations, small rituals, and the way we treat each other when mistakes happen. This piece is about that quieter work.
Private moments that changed my view:
One night I observed my daughter Ellie, hunched over a laptop, twenty tabs open, each promising an answer. The first tab offered a free copy of a textbook. It was the top result – surely a promising solution!
I realized something in that moment. Technical advice rarely reaches people when they are exhausted or pressed for time after a long day of classes or work. The tools and rules exist but are only helpful if they fit into real life, into shortcuts and deadlines, into the small decisions people make while juggling work and family.
Zoie came to me one night asking why a friend had suddenly disappeared from a group chat. She showed me screenshots of messages that looked like account recovery prompts. We walked through the messages together and discovered subtle changes in tone and punctuation that revealed a scam. She was relieved to understand what had happened. She was also quietly proud that she had not reacted by handing over credentials. Those small wins are more powerful than any presentation slide.
From analyst to parent, and what both roles teach me:
Working as a security analyst gave me a map of threats, attack chains, and mitigation strategies. It taught me to look for patterns and to assume adversaries will probe the weakest link. But being a dad refined that map. It taught me how fatigue, embarrassment, curiosity, and convenience shape behavior. It taught me that people do not act in the sterile conditions of lab exercises. They act while caring for younger siblings, rushing to a meeting, or trying to meet a deadline. They act while trying to help a parent or keep a promise.
My parents recently offered a different perspective. I call Mom when I need to slow down and explain things simply. She asks direct questions that cut through jargon. My father asks about the practical outcomes. When I walked my father through how to spot a fraudulent phone call, he said, I wish someone had shown me this years ago. His response reminded me that security advice must be approachable for everyone, not just those comfortable with technology.
My older brother is the kind of person who believes most problems can be solved by asking the right neighbor. He is skeptical of doom-laden headlines and helpful in pointing out when I am overcomplicating a message. His input keeps my language grounded. When I craft tips for students or families I imagine explaining them to him over coffee. That mental audience makes the advice practical.
%20(1200%20x%20800%20px)%20copy%204.jpg)
Simple rituals that actually work:
I have learned that a few predictable habits can reduce a lot of risk. Each Sunday evening I sit with a cup of tea, check for software updates, look at account activity, and confirm backups are running. The ritual takes about fifteen minutes, and it buys calm for the week ahead. It is not dramatic. It is not heroic. It is reliable. I teach this to students not as a strict rule, but as an invitation. Build a ritual that matches your life and your rhythm.
Using unique passwords for each account became feasible for me the day I adopted a password manager. I still remember the first breach notice I received for a service I rarely used. Because I did not reuse credentials, the breach was an inconvenience not a crisis. That feeling of containment is worth the small effort of adopting one secure tool.
When I work with families, I emphasize pauses. Teach kids and colleagues to pause before clicking. Take one breath. Verify the sender. Ask a trusted person. The single act of stepping back interrupts the reflexive click and often prevents harm. Pauses are small and humane. They respect that people are busy and human.
Teaching without shame:
When a student admits they clicked on a phishing link, I respond with a clear recovery plan and an invitation to learn. Shame silences people and prevents the important conversations that follow mistakes. I encourage students to treat incidents as case studies that can be deconstructed without judgment.
I also bring my security analyst stories to class, not as proof of expertise, but as lived examples. One time an alert in a corporate environment pointed to irregular login attempts from a foreign country. We tracked the pattern and found a reused password across a poorly secured service. That incident became a teaching moment, a story about habits rather than villains. Students remember the narrative and the recovery steps more readily than a list of technical controls.
Conversations at home:
My daughters have taught me how to adapt conversations to age and temperament. With Samantha, the oldest, the conversation is about privacy and reputation because she is navigating professional and academic spaces. With Zoie I emphasize skepticism, spotting inconsistencies in messages, and validating sources. Ellie enjoys gaming communities, and our conversations focus on account controls and healthy boundaries. Daymi, younger and curious, benefits from gentle rules and clear explanations about what sharing means in a public space.
It helps to begin as a dialogue with a question. No lectures. I ask what they saw, what surprised them, and what felt uncomfortable. Those questions open discussion and promote cyber safety from curiosity rather than fear. When my daughters come to me with a confusing message or a new app request, we sit together, and we discover together. The search and the discussion teach them how to think about risk.
Supporting older relatives:
My parents call me when they are unsure about a banking email, a caller claiming to be from a utility, or a message that demands immediate action. I cannot assume they adopt every technological control I recommend. Instead, I focus on a few essential protections and on ways to make verification easy.
One night, a caller asked my mother for personal details to correct a records problem. She called me. I guided her through verifying the claim without giving any personal information. We contacted the official organization directly through a published number. Those steps matter because they reduce anxiety for everyone involved and preserve dignity for those who are targeted.
Recovering from mistakes:
If something goes wrong, the response matters. Quick containment, clear steps to recover, and reassurance will reduce harm. When a student in my class had their credentials stolen, we walked through resetting passwords, enabling multi-factor authentication, and reviewing account activity. We also discussed how to inform affected contacts. The immediate technical steps helped recover access. The supportive classroom response reduced the shame and encouraged others to share similar experiences.
Emotional recovery is part of resiliency too. Teach friends and family how to respond if someone is scammed. Offer help, not blame. Guide them through practical recovery steps and, when appropriate, involve financial institutions. The social response can determine whether people seek help or hide incidents out of embarrassment.
%20(1200%20x%20800%20px)%20copy.jpg)
Final thoughts:
Cybersecurity Awareness Month is a useful reminder to inspect our defaults, renew conversations, and refine our habits. It is also an invitation to treat security as a shared human project. Tools matter, frameworks matter, and so do stories. When we lead with empathy, patient explanation, and small predictable rituals, we make security part of ordinary life.
When someone slips up, respond with help, not judgment. When we teach, teach with the real rhythms of life in mind. When we design systems, design for the person who will use them while juggling work, family, and fatigue.
Security is not a test you pass once. It is a set of practices woven into daily life. It is the short pause before you click. It is the conversation with your daughter about why a message looks off. It is the call you make to a parent to verify a strange demand. It is the neighborly nudge from a brother who asks you if you are overcomplicating something. That is where meaningful safety lives.
Rather than a steady stream of cybersecurity reminders in October, we can offer a steady stream of patience and guidance in building secure practices with colleagues, students and loved ones every day.
References
National Institute of Standards and Technology. (2022). Cybersecurity awareness training impact study. U.S. Department of Commerce. https://www.nist.gov/publications/cybersecurity-awareness-training-impact-study
Verizon. (2023). 2023 Data breach investigations report. https://www.verizon.com/business/resources/reports/dbir/
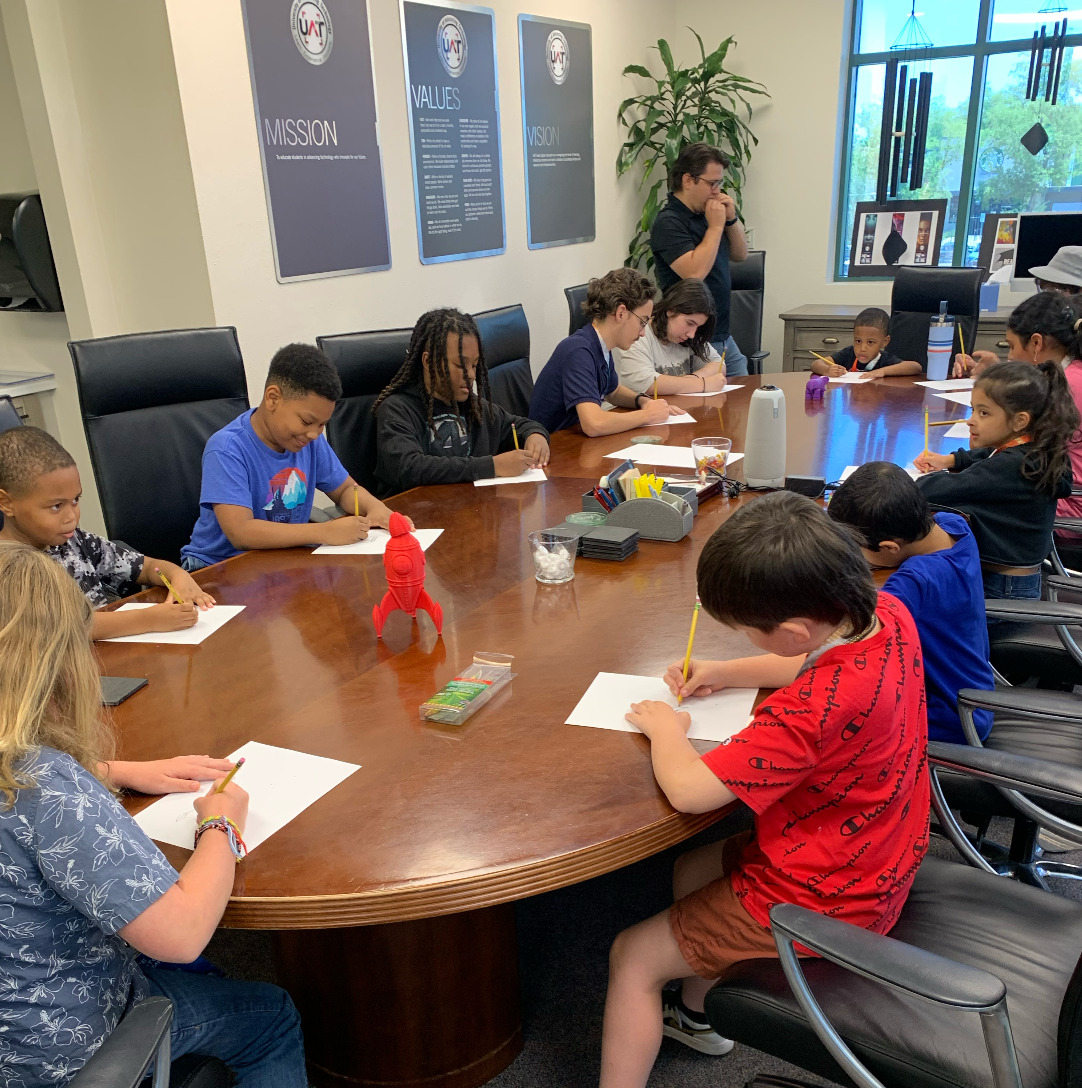
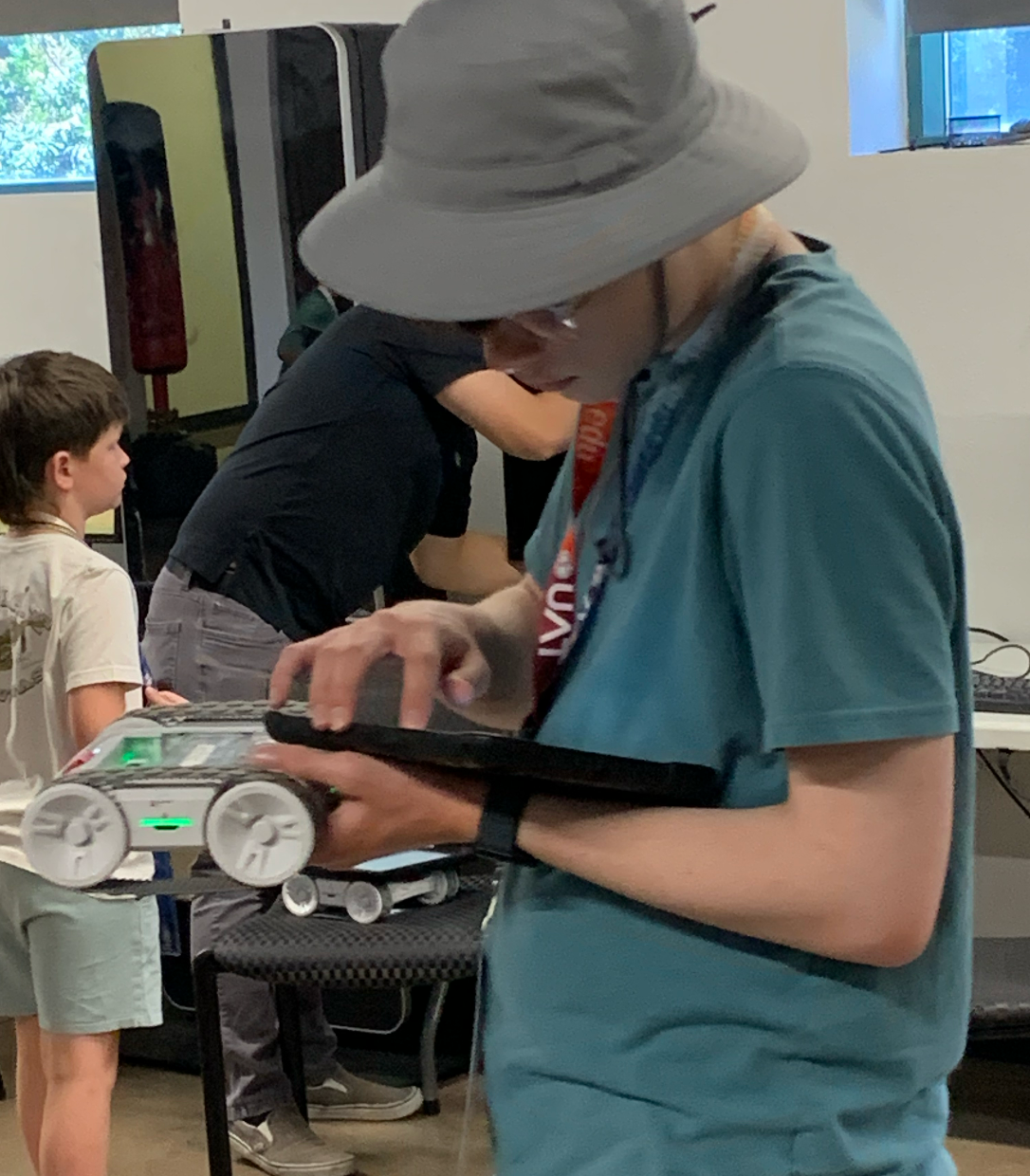
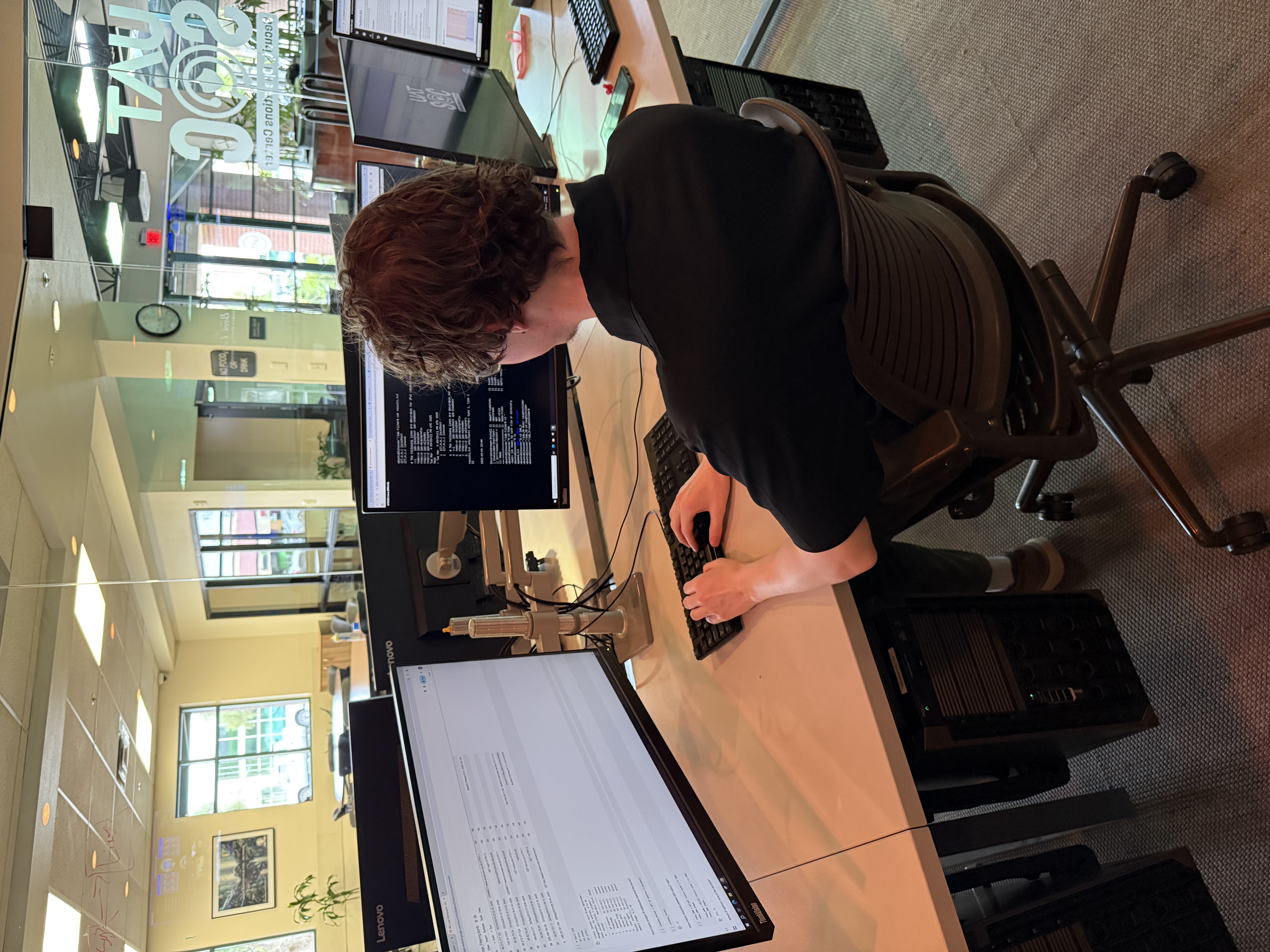
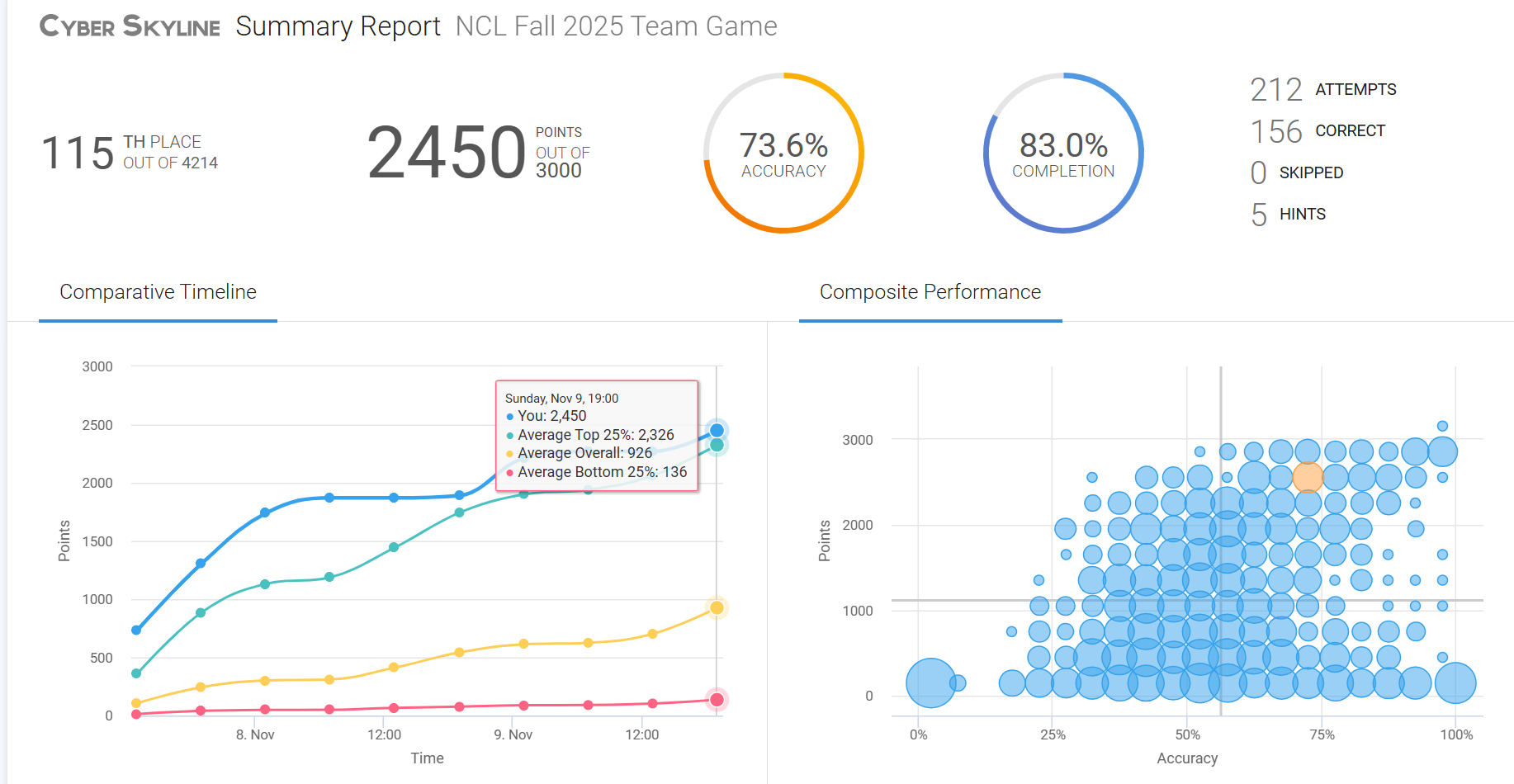
Protect your future in tech — explore UAT's cybersecurity degrees today!








.jpg)




%20(1200%20x%20800%20px)%20copy%204.jpg)
%20(1200%20x%20800%20px)%20copy.jpg)