
ABOUT UAT
University of Advancing Technology is an elite, private college that serves its student body by fostering knowledge creation and academic excellence in an environment that embraces the young technophiles of the world. With three centers of research and a suite of technology-centered undergraduate and graduate degrees, the University is a recognized leader in technology education.

Great games aren’t just imagined — they’re engineered. The Game Programming degree at University of Advancing Technology (UAT) focuses on the architecture, performance, and technical systems that power modern interactive entertainment. Located in Tempe, UAT provides a development-focused environment where students learn to think like software engineers while building real-time games.
Game programmers solve complex technical challenges: rendering thousands of objects in milliseconds, optimizing memory usage, designing Artificial Intelligence (AI) behaviors, synchronizing multiplayer sessions, and ensuring smooth gameplay across hardware platforms. This degree is built for students who want to understand how things work at a systems level — and then improve them.
Unlike programs that focus primarily on design concepts or asset creation, UAT’s Game Programming curriculum emphasizes computer science principles applied directly to game development. Students build strong foundations in data structures, algorithms, object-oriented programming, and software architecture before applying them to interactive systems.
As they progress, students tackle real-time graphics programming, AI, physics simulation, networking, and engine-level problem solving. Performance optimization and debugging are treated as core competencies, not afterthoughts. Students learn how to write efficient code, profile systems, and refine performance — skills that separate hobbyists from professional developers.
Modern games are built by teams, and programmers must communicate clearly across disciplines. At UAT, students collaborate with designers and artists in structured development cycles, contributing technical solutions to fully playable projects. They learn version control workflows, sprint planning, technical documentation, and iterative testing — all essential components of professional studio production.
This hands-on approach ensures students graduate having built real systems under production-style constraints, not just completed isolated programming exercises.
In programming roles, employers evaluate both problem-solving ability and code quality. Throughout the Game Programming degree at the University of Advancing Technology, students build a portfolio that includes playable games, system prototypes, AI implementations, and performance-optimized features. Projects are documented to demonstrate design decisions, debugging processes, and scalability considerations.
UAT’s Career Services team supports students with technical résumé development, GitHub and code portfolio guidance, mock interviews, and career preparation tailored to software engineering and game development roles. Graduates leave prepared to explain not just what they built — but how and why they built it that way.
Graduates are prepared for roles including gameplay programmer, AI programmer, graphics programmer, engine developer, and network programmer. The rigorous technical foundation also supports careers beyond entertainment, including simulation engineering, interactive visualization, virtual reality systems development, and broader software engineering fields.
What degree is awarded?
Students earn a Bachelor of Science in Game Programming from the University of Advancing Technology.
Is this program more technical than Game Design?
Yes. This degree focuses on programming, software architecture, systems development, and performance engineering rather than gameplay concept development.
Do I need previous coding experience?
No prior experience is required, though strong interest in programming and problem-solving is recommended.
Will I build complete games?
Yes. Students contribute to fully playable projects while also developing deep technical systems and prototypes.
Where is UAT located?
UAT is located in Tempe, Arizona, within the Phoenix metropolitan technology corridor.
If you’re ready to move beyond playing games and start engineering the systems that power them, apply to the University of Advancing Technology in Tempe, Arizona or learn more about the Game Programming degree and begin building your future in interactive technology.

During University of Advancing Technology’s (UAT) 2026 Commencement Ceremony, UAT proudly honored Chairman Emeritus Jay Lohman with the Lifetime Impact Award, recognizing decades of dedication, leadership and meaningful contributions to the university’s continued success.
The UAT Lifetime Impact Award is reserved for individuals whose service and vision have made a profound difference over time. Jay Lohman’s enduring support, passion for education and belief in the next generation of innovators make him a truly deserving recipient. UAT founder's Dominic & Ann Pistillo expressed immense gratitude when asked about how Jay has impacted UAT through the years, saying "Rarely in life can you find a man who is so intelligent and wise, but at the same time also loving and giving. Jay Lohman is that exceptional man. Jay is a wise, clever, knowledgeable, and gifted man who is also kind, thoughtful and caring. His open mind, creativity and thirst for constant learning makes him a role model that I look up to and strive to emulate every day. So, thank you Jay for all you mean to our family."
For more than two decades, Jay Lohman has played a transformative role in shaping the future of UAT. Serving on the university’s Board of Directors since 2005 and as Chairman beginning in 2013, his steady leadership helped guide the institution through years of growth, innovation and continued excellence in technology education. When asked about Jay, current Chairman of UAT's Board Jason Konesco said "His expertise in his field and work/life experience overall have greatly advanced UAT's mission over the years as a board member/chair. As much as I've admired his contributions to the board, I must say I most admire Jay because of his character - he is a great listener with a compassionate ear, a person who deeply cares about the conversation at hand and seeks clarity in such, a man of incredible integrity and ultimately someone I genuinely enjoy being around."

Beyond titles and accomplishments, Lohman’s greatest impact has been his investment in people. Known for his generosity, humility and mentorship, he has consistently encouraged students, faculty and fellow leaders to think boldly and lead with integrity. UAT Provost Dr. Dave Bolman highlighted Jay's impact on UAT's senior leadership, stating "a challenge of senior leadership can be having someone to turn to, and each of us from Dominic, to Jason, to myself, to Karla and Valerie have had moments when we could call Jay, he would listen and give us supporting and measured guidance... with a tip of the hat."
As the Class of 2026 celebrated the beginning of their next chapter, UAT is proud to honor a leader whose dedication helped shape the university’s path forward. Jay Lohman’s lasting impact on the university serves as a reminder of the power of leadership, innovation and investing in future generations. His legacy will continue to inspire students to think boldly, pursue their passions and create meaningful change through technology for years to come.
Jay Lohman’s legacy reflects UAT’s commitment to leadership, innovation and student success. Learn more about becoming part of the UAT community.

Leadership is often measured by more than achievements or accolades. It is reflected in the way someone impacts the people around them, lifts others up and creates lasting change through service, mentorship and character. For University of Advancing Technology (UAT) student Aaron Hurst, receiving the Brooke Cayce Legacy Leadership Award represents exactly that kind of responsibility.
“The Brooke Cayce Legacy Leadership Award goes beyond academic achievement; it speaks to something larger and more enduring: character,” Hurst shared. “The Marine Corps built the foundation of who I am, and every day I look for opportunities to elevate the confidence, skill and sense of purpose in the people around me.”
While honored by the recognition, Hurst admitted the award came as a surprise. After learning more about Brooke Cayce’s story and legacy at UAT, the meaning behind the recognition became even more significant. “I researched Brooke’s story, and I gained a deeper respect for what this award means to the university and to the Cayce family,” he said. “I am humbled by her story and honored to be asked to carry her legacy forward.”
That commitment to leadership can already be seen throughout campus. As UAT’s Programming Tutor, Hurst’s involvement with students extends far beyond helping solve coding problems. Instead, he focuses on helping students think critically, ask better questions and develop confidence in their own abilities. “My involvement is daily,” he explained. “I work with students not just to solve problems, but to think more deeply and develop the critical mindset that drives a purpose-driven life beyond the degree.”
Throughout his time at UAT, several faculty members have made a lasting impact on his educational journey. Professors Tony Hinton, Rae Crusoe and Rawad Habib stood out for both their knowledge and the care they show students inside and outside the classroom. “I have gained more knowledge in computer science under their instruction than at any previous institution, and that is not a small statement,” Hurst said.
He also spoke highly of Dr. Matthew Prater, whose dedication to both students and family left a strong impression. “He elevates the people around him because that is who he is,” Hurst shared. “Frankly, he should be the one answering these questions. He is exactly what leadership at UAT looks like.”
When reflecting on memorable moments at UAT, Hurst didn’t point to awards, projects or competitions. Instead, he highlighted the people who shaped his experience.
He recalled working with fellow students like Anique Daugaard, whose determination as an online student, wife and mother continues to inspire him, and Makayla Barclay, whose relentless curiosity pushed conversations beyond finding answers and into truly understanding technology. He also reflected on Camden Copeland’s growth from needing help with assignments to independently building and presenting a final project. “Watching that shift happen in real time was one of the most rewarding experiences I have had at UAT,” he said.
Perhaps most impactful were Michael Garcia and Joe Haskins, fellow students and veterans who welcomed him into collaborative projects early in his UAT experience.“They taught me, challenged me and met me exactly where I was in my education,” Hurst shared. “The best leadership rarely announces itself.”
Before arriving at UAT, Hurst admitted he carried doubts after a difficult experience at another university. He questioned whether he belonged and whether he would truly grow in the field he was passionate about. That perspective quickly changed.“I was dead wrong,” he said. “I have learned more about programming, computer science, AI and robotics here than anywhere I have ever been.”
That growth inspired him to expand his academic path, adding Robotics Engineering and Artificial Intelligence to his studies and pursuing a triple degree including Advancing Computer Science. After graduation, he plans to continue into UAT’s Master’s degree in Technology Innovation.
“This place changed the trajectory of what I believe is possible,” Hurst said. “I intend to honor that.”
The Brooke Cayce Legacy Leadership Award recognizes students who embody leadership through service, integrity and impact on others. Through mentorship, perseverance and a commitment to elevating those around him, Aaron Hurst is continuing that legacy in meaningful ways every day.
Explore UAT Degrees designed to help students lead the future of technology.

As automation, Artificial Intelligence (AI), and smart systems continue to transform global industries, robotics engineering has emerged as one of the most impactful and future-focused technology fields. The Robotics Engineering Degree at University of Advancing Technology (UAT) prepares students to design, build, and program intelligent machines that solve real-world problems across manufacturing, healthcare, aerospace, defense, and logistics.
Located in Tempe, Arizona, UAT delivers a hands-on, project-based robotics education designed for students who want practical experience with emerging technologies—not just theory.
Robotics engineering is a multidisciplinary field that blends mechanical engineering, electrical engineering, computer science, and artificial intelligence. Robotics engineers create autonomous and semi-autonomous systems capable of sensing, decision-making, and action. These systems range from industrial robotic arms and mobile robots to drones, medical devices, and autonomous vehicles.
Through robotics engineering, students learn how hardware and software work together to create intelligent machines that interact with the physical world.
Robotics engineering plays a vital role in modern innovation as industries increasingly rely on automation to improve efficiency, accuracy, and safety. Organizations across sectors are investing in robotics solutions to streamline operations, reduce costs, and expand technological capabilities.
From advanced manufacturing and warehouse automation to medical robotics and aerospace exploration, robotics engineers are driving progress in high-growth fields. As automation and AI adoption accelerate, demand for skilled robotics professionals continues to rise—making a robotics engineering degree a strong long-term career investment.
University of Advancing Technology emphasizes experiential learning through a technology-first curriculum. Students pursuing a Robotics Engineering Degree actively design, prototype, and test robotic systems throughout their coursework, working hands-on in UAT’s Engineering Lab equipped for building, programming, and refining real-world robotic applications. Rather than focusing solely on exams, students graduate with practical experience and project portfolios that demonstrate real technical ability and industry-ready skills.
UAT’s location in Tempe, Arizona places students near the Phoenix metro area’s expanding tech ecosystem, offering access to industry connections, internships, and career opportunities in robotics, automation, and engineering.
Through the carefully curated curriculum, students develop a broad skill set that combines engineering fundamentals with advanced robotics applications. Coursework focuses on both hardware and software integration, allowing students to understand how sensors, actuators, control systems, and AI-driven logic work together.
Graduates leave prepared to program autonomous systems, design mechanical and electrical components, integrate intelligent sensors, troubleshoot robotic performance, and adapt to evolving technologies in the field.
A robotics engineering degree opens doors to careers across multiple industries that rely on intelligent automation. Graduates are prepared for roles that involve designing, maintaining, and improving robotic systems used in real-world environments.
Robotics Engineer
Automation Engineer
Embedded Systems Engineer
AI & Robotics Developer
Mechatronics Engineer
These career paths offer opportunities both within Arizona’s growing tech sector and across national and global markets.
1. What can you do with a robotics engineering degree?
Graduates can pursue careers in robotics, automation, AI development, manufacturing, aerospace, healthcare technology, and related engineering fields.
2. Is robotics engineering a good career choice?
Yes. Robotics engineering is a fast-growing field with strong job demand driven by increased automation and artificial intelligence adoption.
3. Does UAT offer hands-on robotics projects?
Yes. UAT’s robotics engineering curriculum is project-based, allowing students to build and test robotic systems throughout the program.
4. Where is the University of Advancing Technology located?
UAT is located in Tempe, Arizona, near the Phoenix metro area’s growing technology industry.
5. Do I need prior robotics experience to enroll?
No prior robotics experience is required. The program is designed to develop skills from foundational concepts through advanced robotics applications.
If you’re ready to design intelligent machines and contribute to the future of automation and AI, the Robotics Engineering Degree at the University of Advancing Technology provides the hands-on education needed to succeed.
👉 Explore the Robotics Engineering Degree
👉 Apply to UAT and start your robotics engineering journey today

At University of Advancing Technology (UAT), innovation, creativity and determination are at the heart of every student journey. This year, UAT is proud to recognize Preston Chapman as the 2026 Valedictorian, honoring his hard work, academic excellence and dedication throughout his time at the university. When he was notified of this recognition for this year's Commencement ceremony, Preston said "It was a lot of emotions, I'm accepting it with great honor. It's something I'm happy to have but it wasn't something I was expecting."
Since coming to UAT in the Fall of 2023, Preston pursued a double major in Advancing Computer Science and Network Engineering, demonstrating both technical skill and a passion for solving complex challenges. Throughout his time at UAT, he consistently pushed himself to grow as a student, innovator and leader while balancing the demands of two rigorous degree programs. He was not only a leader in the classroom but also on campus, working as a computer science tutor helping his fellow students when they needed it. Assistant Director of Student Services Ashley Fuentes said "Preston is reliable, supportive, and genuinely cares about the success of others."

Earning the title of Valedictorian reflects not only Preston’s academic achievements, but also his perseverance and drive to innovate. Faculty and fellow students alike recognize him for his positive attitude, leadership and willingness to support those around him. Professor Rae Crusoe highlighted Preston, saying "Preston was a joy to have in my classes! He always came to class ready to learn and explore ways to make his programs better. I can't think of an assignment where he did not add something above and beyond the requirements to truly embrace the role of software engineer. Preston was always willing to help other students both in class and as a tutor."
As he begins the next chapter of his journey, Preston represents the future of the tech industry — creative, motivated and ready to make an impact. On UAT's Tech Respect Podcast, when asked what's next for him, Preston said "I know I have a lot of options which is why I went with a double major, I wanted to give myself as many options as I can. I'm working on my website and getting my portfolio and LinkedIn page up to date. Then start applying in the next few weeks."
Congratulations to Preston on this incredible achievement and for leading the Class of 2026 with excellence. Everyone at UAT looks forward to seeing all that he accomplishes in the years ahead.
Ready to innovate, create and lead? Explore what makes the UAT student experience unique. Learn More today!

What an incredible semester we've had! As we wrap up the spring term, I wanted to share some of the amazing achievements and developments that made the first part of 2026 memorable.

A Historic Start to 2026
On February 14 our official mascot Wrath the Wyvern landed; you can read his origin story at uat.edu/wrath. Don’t worry, though! Max our resident “catscot” is still hanging around the Quad.
After starting the year with a game jam, February also brought our AZStruT Refurbishing event. At this event, UAT students refurbished over 75 computers for the Cartwright School District, making a difference for hundreds of students across the Maryvale district.
A major theme of this semester was competition, and our students absolutely delivered. During Arizona Tech Week, our teams dominated multiple events:
Looking Ahead
True to our Mission, we're constantly upgrading our campus. The Founder’s Hall movie theater was renovated last month, and the summer semester will bring students a brand new Manufacturing Innovation Lab which will house a Tormach 770 commercial CNC mill.
Ahead of the 2026 Commencement Ceremony, we’re excited to host Honorary Doctorates Dara Gibson (CEO, Cybersecurity Readiness Advisors) and Austin Carson (Founder, SeedAI) for dinner with students that are part of our prestigious Honors program.
The summer term is packed with opportunities! We have camps, community projects, and our Vibe Coding Jam in June. Whether you're a current student or considering UAT, there are plenty of ways to get involved.
Congratulations to the UAT graduating class of 2026!

Valerie Cimarossa
Chancellor, University of Advancing Technology

The Spring 2026 Student Innovation Project (SIP) Showcase at University of Advancing Technology (UAT) was a powerful celebration of creativity, collaboration and future-focused thinking. Students from across multiple technology disciplines came together to present the projects they’ve spent months designing, building and refining. From immersive games and intelligent systems to robotics, cybersecurity solutions and digital experiences, the showcase highlighted the innovation and determination that define the UAT community. Here’s a recap of the standout moments, inspiring ideas and student achievements that made this semester’s showcase one to remember.

Garden Share - Ashley Kennedy - WORLD CHANGER + VIEWER'S CHOICE AWARD WINNER
A platform designed to reunite neighborhoods where neighbors grow and trade produce in an effort to alleviate dependence and the cost of shopping at grocery stores. The application includes a farmers market where you can post your produce as well as search what neighbors are trading, a recipe page where you can post and search for recipes, AI Plant identification and more.
Origin Guess!! - Nichole Losh
A game for people to learn about AI and AI literacy. It's an interactive and engaging game that teaches its players about AI using fun features like the ability to play at different levels, compete on a leaderboard and more.
AI Buddy - Anthony Mercer
An AI solution, designed to transform how customers interact with a website. A personalized AI shopping assistant that creates a digital avatar to represent users online. It improves the shopping experience by offering tailored recommendations and real time help, making online shopping faster, easier and more human.
Ant-AI - Magaly Valdez
A website and application that can determine if an image is AI generated.

PreVis Street - Noah Walker - BEST IN SHOW AWARD WINNER
A storyboarding tool that lets you plan shots using real world environments, rather than hand drawing each shot.
Fate Finder - Zyriah Stoker
An AI powered application that helps users discover and research their belief systems through asking keep thought based questions. Designed for those who are searching, questioning, or unsure of their belief systems.
5 Stars + Bot - Andrew Lucier
A professional wrestling website and chat bot to help predict the outcome of professional wrestling matches.
Iterum AI - John Arcagua
An AI application to preserve the personality of a deceased loved one. Designed to preserve memories, voice, personality and interaction. This app turns them into a digital bot that would allow loved ones to interact with their deceased loved one.
AI Network Anomaly Dashboard - Nasser Altaey
A real-time web based security monitoring tool that uses AI to watch network traffic, detect threats, and show them in a way that anyone can understand and act on.
IoT Armor - Christopher Woods
A tool intended to help users identify network security risks associated with smart devices.
Scoot Alert - Marcus Frazier
An automatic system for activating bike horns.

Shine N' Go - Jaylan McCoy - BEST SIP PITCH + VIEWER'S CHOICE AWARD WINNER
A smart shoe care cleaning system, designed to make cleaning faster, safer and hands free.
The Turtle Brush - Calvin Harding
A robotic dishwashing brush designed to make handwashing dishes easier.
Snapper -Andrew Headrick
A 2-factor clapper switch for your lights, this requires two triggers to turn the light on and off rather than the old school clapper which only triggered on audio queue. Snapper will trigger the lights with one audio and one motion que.
NBED TV Mount - Stephan Hammonds - INGENUITY PRIZE WINNER
An electronically adjustable tv mound for the bedroom. Instead of constantly adjusting yourself or pillows to see the tv comfortably in bed. this mount will dynamically position the screen above the bed to allow the user to maintain and ergonomic position.
Sky Factor Customized Mouse - Jonathan Coleman
A custom computer mouse designed to form fit to the users unique hand.
Marchy - James Patton - MOST MARKET VIABLE AWARD WINNER
A flexible interface that attaches the mouth piece of a brass intstrument to the body of the intstrument, allowing the mouth piece to flex, making it more comfortable for the user to play.
Exbloom - Natalie Caraway
A falling block puzzle game. Rather than the traditional game where blocks clear when 3 or more of the same color touch, in this new game the user will place the pieces until the timer hits 0. Then and explosion, where only the pieces that are not 3+ touching remain, and you continue to play the board until the next timer goes off.
Long Time Tutorial Plugin - Mason Griffith
This application measures how long you have been away from a game for. If the days pass hits a threshold named by the developer, the plugin runs a refresher on the game for the user.
Ventura - Benton Marcum
A language learning game, users learn language by playing an open world exploration experience game. The player helps the main character explore and reconnect with his rood, learning the language and culture withe the character.
Meditation Aura Visualizer - Brain DeNeffe
An application that takes current mood and transforms it into light, colors and sound using simple math.
Ready to build what’s next? Learn more about UAT degree programs today.

Virtual reality is reshaping how people learn, train, design, and interact with technology. As immersive experiences become standard across industries, earning a Virtual Reality degree helps students build future-ready technical and creative skills.
University of Advancing Technology (UAT) offers a career-focused Virtual Reality (VR) degree for students who want to design interactive digital environments. Located in Tempe, Arizona, UAT places students near the expanding Phoenix tech and gaming ecosystem, offering access to innovation, collaboration, and career opportunity.
A Virtual Reality degree focuses on designing and developing immersive digital experiences using modern tools and workflows. Students gain a blend of technical, creative, and problem-solving skills.
At UAT, key courses students will take include:
GAM101 Introduction to Game Design
HCI 101 Introduction to Human Computer Interaction
VRT101 Introduction to Virtual and Augmented Reality
VRT310 Virtual Environments
VRT330 Augmented Reality Development
VRT456 AR Applications and Ethics
UAT’s project-based learning model ensures students graduate with hands-on experience and a professional portfolio.
Virtual reality technology continues to expand far beyond entertainment, with industries increasingly adopting immersive tools to enhance training, communication, and visualization. A Virtual Reality degree prepares students to contribute to fields such as gaming and interactive media, healthcare and education, simulation training, architecture, engineering, and emerging technology. These adaptable, future-focused skills help graduates remain competitive as immersive technologies continue to evolve.
University of Advancing Technology offers a technology-first learning environment built around innovation and real-world application. UAT’s Virtual Reality degree stands out through hands-on, project-based coursework, interdisciplinary collaboration with Game Design and Software Engineering students, and close proximity to the growing Phoenix metro tech industry. This immersive approach mirrors professional development environments and prepares students with the skills and experience needed for modern technology careers.
Graduates of UAT’s Virtual Reality degree program are prepared for careers that blend creativity with advanced technology.
Common career paths include:
Virtual Reality Developer
Simulation or Training Designer
UX Designer for immersive platforms
As immersive technology adoption grows, demand for VR-skilled professionals continues to rise.
What careers can you pursue with a Virtual Reality degree?
Graduates can work in VR development, simulation design, user experience design, interactive media, and emerging technology roles.
Is a Virtual Reality degree worth it?
Yes. Virtual reality skills are in demand across industries such as healthcare, education, defense, architecture, and entertainment.
Where is University of Advancing Technology located?
UAT is located in Tempe, Arizona, within the greater Phoenix technology corridor.
Does UAT offer hands-on Virtual Reality experience?
Yes. UAT emphasizes applied, project-based learning so students graduate with real-world experience and professional portfolios.
Do students need prior VR or coding experience to enroll?
No. UAT’s Virtual Reality degree is designed to teach foundational skills and build expertise throughout the program.
How does UAT help students prepare for VR careers?
UAT focuses on portfolio development, real-world projects, interdisciplinary collaboration, and industry-aligned coursework.
Turn your passion for innovation into a career with the Virtual Reality degree at University of Advancing Technology. Learn by doing, collaborate with tech-driven peers, and build a professional portfolio in Tempe, Arizona, near the heart of the Phoenix tech ecosystem.
Explore the Virtual Reality degree and start your journey at UAT today.

The University of Advancing Technology (UAT) was proud to participate in Tempe’s 12th annual STEAM Festival, Geeks Night Out, a signature event of the Arizona SciTech Festival.
Held in partnership with the City of Tempe and supported by organizations like State Farm and the Tempe Diablos, Geeks Night Out transformed the city into an interactive playground for learners of all ages. UAT joined more than 60 organizations in delivering engaging exhibits and activities, providing a firsthand look at the exciting intersections of technology and creativity.
At UAT’s booth, attendees had the opportunity to explore cutting-edge technology, including robotics, coding exercises, and virtual reality experiences. Our faculty and students engaged with curious minds, demonstrating how innovation shapes the future. Whether experimenting with AI, diving into game development, or learning about cybersecurity, visitors got a taste of what makes UAT a leader in advancing technology education.

As an institution dedicated to fostering technology-driven education, UAT values opportunities like Geeks Night Out to connect with local schools, businesses, and fellow higher education institutions. The event’s collaborative spirit—bringing together Tempe Elementary School District, Tempe Union High School District, Kyrene School District, East Valley Institute of Technology (EVIT), Arizona State University, and Rio Salado College—reflects a shared commitment to preparing future innovators.
For those who visited our booth—thank you for geeking out with us! If you’re interested in UAT's upcoming Future Innovators Camp from June 22nd to 27th for students ages 6-16, click here for more information.
Follow Tempe Geeks Night Out on Facebook and Instagram to get excited for the event!

The Game Design degree at University of Advancing Technology (UAT) prepares students to become the creative architects behind today’s most engaging interactive experiences. Located in Tempe, UAT offers a technology-focused campus environment where students learn to design gameplay systems, mechanics, and immersive worlds that captivate players across console, PC, mobile, and emerging platforms.
Game designers are responsible for more than ideas — they build systems that function. From level progression and player psychology to balancing mechanics and narrative integration, UAT’s Game Design degree teaches students how to turn concepts into playable, engaging experiences grounded in both creativity and technical understanding.
At UAT, students move beyond theory and into production. The curriculum emphasizes systems design, level design, mechanics development, storytelling, and player experience. Students learn how to document ideas clearly, prototype gameplay quickly, and refine their work through testing and iteration — essential skills in professional studio environments.
Collaboration is a core component of the program. Game Design students work alongside programmers and artists to build functional prototypes and complete playable projects. This cross-disciplinary approach mirrors real-world development pipelines and ensures graduates understand how design decisions impact art, code, performance, and player engagement.
Throughout the degree, students develop expertise in:
In the game industry, designers are hired based on what they can build — not just what they can describe. That’s why portfolio development is embedded throughout the Game Design degree at the University of Advancing Technology. Students begin creating playable prototypes early in the program and refine them through critique, iteration, and collaborative production cycles.
Through real-world team experiences, students graduate with a portfolio of documented systems, level designs, and fully playable projects that demonstrate both creative vision and structured design thinking. UAT’s Career Services team supports students with portfolio reviews, résumé guidance, and interview preparation, helping graduates confidently present their design process and problem-solving abilities to studios and interactive media employers.
The skills developed in the program also transfer into related industries including simulation, immersive media, serious games, and interactive storytelling. Graduates of UAT’s Game Design program are prepared for roles such as:
What degree is awarded?
Students earn a Bachelor of Arts in Game Design from the University of Advancing Technology.
Do I need programming experience?
No prior programming experience is required. The program introduces technical concepts alongside design principles.
Will I build playable games during the program?
Yes. Students create prototypes and full playable projects throughout the curriculum.
Is collaboration part of the degree?
Absolutely. Students work with programmers and artists in team-based development environments.
Where is the program located?
The Game Design degree is offered on campus in Tempe, Arizona, within the Phoenix metropolitan area.
If you’re ready to turn your creativity and strategic thinking into a career in interactive entertainment, apply to the University of Advancing Technology in Tempe, Arizona or learn more about the Game Design degree and begin building your future in game development today.


Each year, National Dissertation Day celebrates the persistence, curiosity, and deep thinking required to complete a dissertation. While that milestone represents the peak of formal academic research, the mindset behind it—questioning, evolving, and pushing knowledge forward—is what truly matters. At University of Advancing Technology (UAT), that mindset extends beyond the classroom. It’s reflected across both faculty and staff, creating a campus-wide culture where continuous learning isn’t just encouraged—it’s expected.
UAT’s degrees span everything from Network Security and Artificial Intelligence to Game Programming and Robotics Engineering—fields that evolve constantly and require educators and staff who evolve with them.
Faculty like Dr. Briant Becote bring advanced research and real-world insight into cybersecurity programs, while Dr. Hue Henry applies innovative thinking to game studies and interactive learning. In robotics and autonomous systems, Dr. Matt Prater helps students explore how intelligent machines interact with the physical world—bridging software, hardware, and real-world application.
Dr. Prater emphasized why continuing education is important and how his experience in the dissertation process impacts his teaching, saying "The only constant is changes the one only way to keep up with change is education, and I tend to approach things more systematically after going through the PhD process."
Communication and critical thinking are reinforced by educators like Dr. Daniel Pike and Dr. Ellen Wolterbeek, while staff across departments help students translate those skills into career readiness—from resumes and portfolios to real-world application.
This culture of continuous learning is especially impactful within UAT’s graduate degrees, where advanced concepts meet real-world application. Students benefit from guidance shaped by experienced educators like Dr. Mark Smith and UAT Provost Dr. David Bolman, whose leadership helps ensure the curriculum remains innovative, relevant, and aligned with industry needs.
When asked how his PhD impacts UAT students Dr. Bolman stated "My PhD research was partly about identifying technology trends so that organizations have the tools and people trained in building their product portfolios and infrastructure so they are ready right at the moment when an emerging tech becomes mainstream. I teach these same techniques in MS649 Technology Forecasting and Change Management. The rest of my doctoral research involved what kinds of leadership techniques help the most when leading technology teams and creative builders. UAT students get to hear about these techniques whenever I teach MS624 Managing People in a Technology Environment."
Dr. Smith brings his experience with the dissertation process into his classroom, he said "The dissertation process was the main aspect of my program that made me a better professor. The amount of work, iterations, research and constant criticism that came with it allows me to be more connected to my students. As a lifelong learner myself, I can empathize with them and understand all the challenges that come from being a student myself."
Beyond academics, staff play a critical role in supporting graduate and undergraduate students alike—helping them navigate their education, refine career goals, and prepare for what comes next. From admissions to student services, UAT’s teams work together to create an environment where students can thrive.
What makes UAT unique is that the commitment to learning isn’t limited to teaching—it’s embedded across the entire university.
Faculty members such as Dapzury Valenzuela, Jake Perrine, Tony Hinton, Adam Zeiner, and Rawad Habib are actively pursuing their doctoral degrees while continuing to teach and mentor students. Their journeys reflect the same perseverance and curiosity that National Dissertation Day celebrates.
Professor Perrine highlighted his PhD experience, stating "Pursuing my PhD in Biomedical Engineering has been an amazing opportunity to stay at the forefront of emerging biotechnologies, while also being a wonderful way to continue to fuel my passion for bioengineering. This has helped me as a Professor to bring the latest advancements in the field to the classroom. This includes the newest biotechnology, best practices in biotech design, and even some of the coolest discoveries from the most recently published studies in biomedical engineering."
Professor Habib reiterated that lifelong learning is a constant here at UAT, stating "Starting my PhD this fall reflects my belief that learning never stops. Continuing my education allows me to bring the latest research, deeper technical knowledge, and real-world problem solving approaches into the classroom so students benefit from both current industry practices and emerging ideas."
That same drive extends into university leadership and staff. Dean of Faculty Allyson Videtic and VP of Student Affairs Brandi Beals are also pursuing their PhDs, demonstrating that growth and development are priorities at every level of the institution—not just in the classroom, but in how the university supports and serves its students. Brandi described how earning her EdD will impact UAT students "Continuous learning drives innovation, strengthens leadership, and ultimately improves student success — making the pursuit of continuing education one of the most valuable investments I can make. This investment isn’t just in myself; it’s in the students and communities I am privileged to serve."
Across campus, this culture of lifelong learning shows up in meaningful ways:
National Dissertation Day is ultimately about the pursuit of knowledge—and at UAT, that pursuit is shared across an entire community.
Faculty bring expertise and evolving insight into the classroom. Staff create the structure and support that allow students to succeed. Leadership models what it means to keep growing. Together, they create a university culture rooted in curiosity, adaptability, and forward momentum.
At UAT, learning doesn’t stop with a degree—it’s a mindset that shapes everything.
Join a university built on continuous learning—explore UAT and apply today.
At the University of Advancing Technology (UAT) in Tempe, Arizona, students learn real world skills that showed and shined in two key valley competitions.
Arizona’s AZTech Week brought together some of the most forward-thinking minds in the state—and students from the University of Advancing Technology (UAT) stood out in a big way, earning top honors in two separate competitions that highlight both applied AI innovation and foundational research.
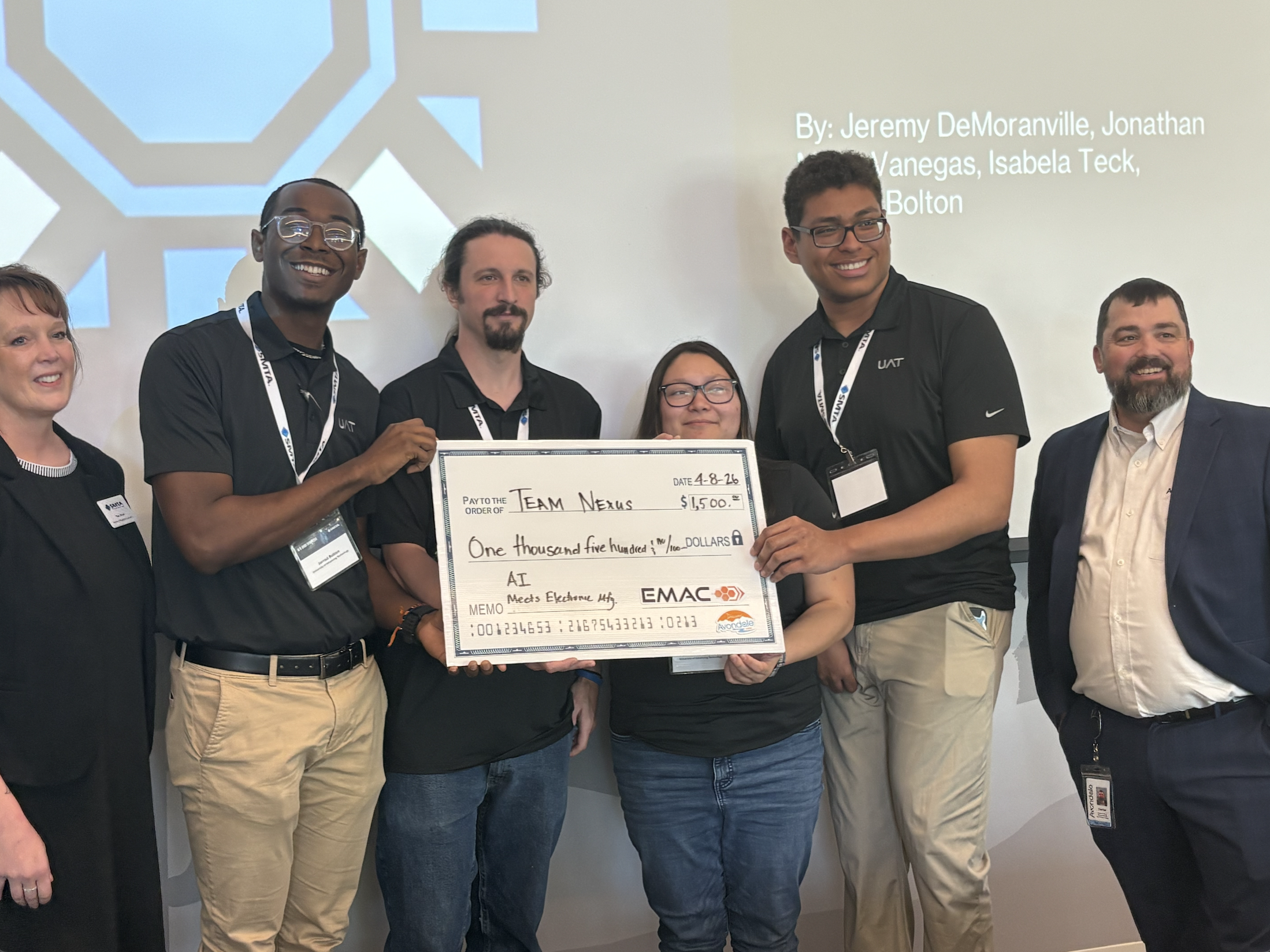
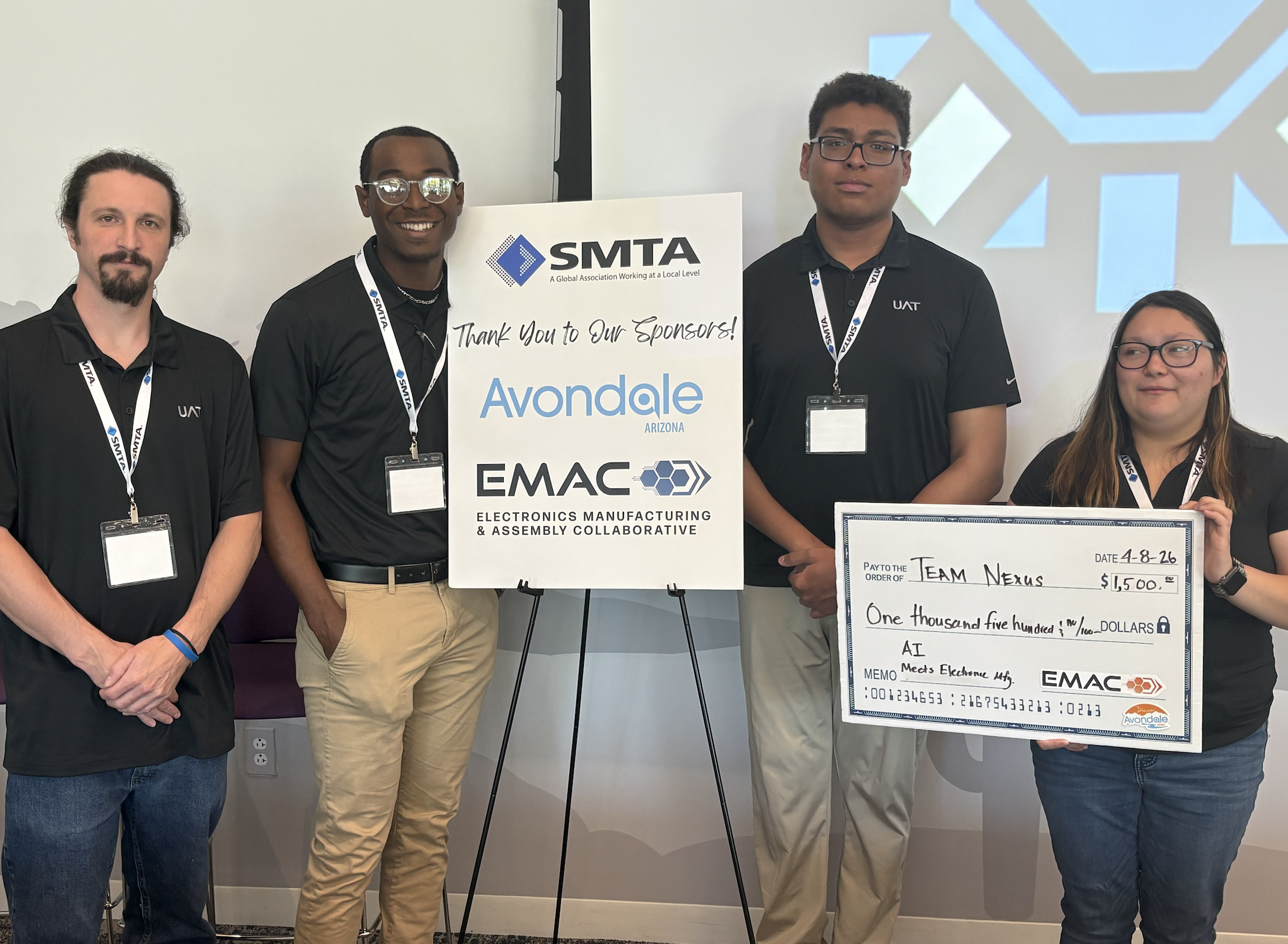
At the Student Technology Showcase, Team Nexus from UAT took first place with a highly relevant and technically ambitious solution focused on supply chain visibility.
The team—comprised of Jeremy Demoranville, Jerrod Bolton, Isabela Teck, and Jonathan Mejia-Vanegas—had just one month to design and build an agentic AI-driven application addressing one of today’s most complex industry challenges: supply chain uncertainty.
Their solution targeted real-world issues including material availability, regulatory compliance, counterfeit risk,logistics constraints, and supplier performance. The system integrates probabilistic risk scoring, supplier risk analysis, and an automated procurement workflow designed to support earlier and more informed design and sourcing decisions.
The result is a practical, forward-facing tool aimed at reducing risk and improving efficiency in enterprise supply chains—potentially saving significant time and cost at scale
UAT also earned top honors at the AZ Research and Innovation Expo, hosted at UAT, where Team UAT received the University Prize for their project BeforeTech: The Physical Foundation for Digital Lives.
The project explores the often-overlooked physical systems and infrastructure that enable digital environments to function—connecting the tangible world to the digital experiences we rely on every day. It reflects a deeper systems-level understanding of how technology is built, supported, and sustained.

These wins reflect more than competition success—they highlight the depth of thinking, speed of execution, and applied innovation happening within UAT’s student community.
From AI-driven enterprise tools to foundational research on digital infrastructure, UAT students continue to demonstrate what it looks like to move ideas from concept to impact.

Join the winning culture and become a UAT student today. Learn more here.

In today’s digital economy, data drives nearly every industry. From cybersecurity and healthcare to finance, Esports, and entertainment, organizations depend on professionals who can transform raw information into actionable insight. A Data Science degree at University of Advancing Technology (UAT) prepares students with the technical expertise, analytical mindset, and hands-on experience required to lead in this data-driven world.
Located in Tempe, UAT places students at the center of Arizona’s growing technology corridor, offering access to innovation, internships, and industry collaboration.
Data science sits at the intersection of programming, statistics, artificial intelligence, and business strategy. Companies aren’t just collecting data — they’re competing on it. Organizations need professionals who can:
A Data Science degree provides structured, in-demand training that employers actively seek. Graduates leave prepared to analyze trends, forecast outcomes, and design intelligent systems that improve operations and innovation.
At the University of Advancing Technology, learning goes beyond theory. Students work on real-world projects, collaborate across disciplines, and develop portfolios that demonstrate measurable results.
Key skill areas include:
Because UAT is a technology-focused university, Data Science students often collaborate with peers in cybersecurity, game development, robotics, and software engineering — mirroring how cross-functional teams operate in industry.
 Career Opportunities with a Data Science Degree
Career Opportunities with a Data Science DegreeThe demand for data professionals continues to grow nationally and globally. Graduates with a Data Science degree can pursue roles such as:
Arizona’s expanding tech ecosystem — particularly in the greater Phoenix and Tempe area — creates local opportunities while also preparing students for national and remote positions.
A Data Science degree from UAT helps students develop highly searchable, resume-boosting skills, including:
These competencies align with current job market demands and position graduates for long-term career growth.
Choosing a Data Science program in Tempe offers geographic advantage. The Phoenix metro area is home to startups, Fortune 500 companies, and emerging tech firms investing heavily in analytics and automation.
The University of Advancing Technology integrates industry relevance directly into its curriculum. Students graduate with not just a degree, but a project-based portfolio that demonstrates applied problem-solving — a major differentiator in competitive job markets.
AI automation, and data-driven decision-making are reshaping industries. A Data Science degree equips students to design the systems behind these innovations rather than simply use them.
As organizations rely more heavily on predictive modeling and intelligent automation, professionals who understand both the technical and strategic aspects of data will lead the next wave of digital transformation.
Graduates can work in roles such as data scientist, machine learning engineer, business intelligence analyst, or AI developer across industries including healthcare, finance, gaming, cybersecurity, and technology.
Yes. Data science remains one of the fastest-growing technology fields due to the rapid expansion of AI, automation, and big data across nearly every industry.
Yes. Students complete project-based coursework and develop portfolios that demonstrate real-world application of analytics and machine learning.
While prior experience can be helpful, many programs introduce foundational programming skills before advancing into complex analytics and AI development.
The University of Advancing Technology is located in Tempe, Arizona, within the Phoenix metropolitan technology corridor.
Data powers the modern world — and the professionals who understand it shape the future. A Data Science degree from the University of Advancing Technology provides the technical depth, industry relevance, and hands-on experience needed to thrive in today’s innovation economy.
Apply now to UAT or learn more about the Data Science degree program and start turning data into impact.

At the University of Advancing Technology (UAT) in Tempe, Arizona, even the campus cat has a title.
His name is Max, and around campus he's known as the university's Senior Purrformance Analyst.
It's a tongue-in-cheek role, of course - but Max has become a genuinely memorable part of campus life. During tours, visitors often pause mid-conversation to ask:
"Wait, is that the cat?"
Phones come out. Photos get taken. Someone crouches down for a quick scratch behind the ears. For a moment, the lab relaxes.
According to UAT admissions staff, Max has quietly become one of the most photographed moments during campus visits. Tour groups often stop to take pictures or ask where he might appear next, making him an unexpected ambassador for UAT's hands-on tech culture.

Walk through UAT's project spaces late in the afternoon and you'll see students deep in their work:
Then Max wanders through.
He stretches across a keyboard.
He settles onto a stack of papers.
He claims the warmest laptop in the room.
Students laugh, adjust their workspace, and keep going.
It's a small interruption - but it reflects something important about how learning works at a university built for builders.

UAT has never tried to be a traditional, lecture-heavy institution built around distance and ceremony. It's a hands-on STEM university in Arizona where students begin building real systems early in their degree programs.
Students collaborate across disciplines, prototype ideas quickly, and learn by testing and iterating in public.
Projects evolve. Systems break. Teams adapt.
In that environment, the occasional disruption - even from a campus cat - becomes part of the rhythm of real work.
A cat wandering into a cybersecurity lab and sitting on sensitive documents might feel like a joke, but it mirrors a lesson students learn quickly in technology careers:
Systems rarely behave exactly as planned. Adaptability matters.

In 2026, as artificial intelligence and automation reshape industries, the value of a tech degree is increasingly about more than memorizing tools. Employers need professionals who can:
That mindset is built into the UAT learning model. Students don't just learn how to use today's technology - they learn how to interrogate systems, understand why something works, and redesign it when it doesn't.
Max, in his small soft-footed way, reinforces the point. He forces people out of autopilot. He introduces randomness into rigid workflows. And he reminds students that attention is a resource - and that how you respond when you're disrupted says a lot about whether you truly understand what you're doing.

At UAT, weird is not a liability. It is a signal. It means something new might be happening. It means someone is testing an idea that doesn’t yet have a name. It means a student might be on the edge of discovering something important.
Max does not know any of this, of course. He just knows where the warm keyboards are, which humans give the best scratches, and how to position himself in the center of whatever is happening.
Which, come to think of it, is exactly what great institutions do too.

UAT students study and build in fields like:
Across these programs, curiosity isn't treated as a distraction. It's treated as the engine.
Max may be a cat. But he's also a small, living reminder of what UAT does best: building environments where creativity and innovation are part of the daily operating system.
Explore Technology Degrees at UAT
If you're ready to build, break, and rethink the future of technology, explore UAT's degree programs and experience the campus culture in person.
Schedule a campus tour and see why curiosity isn't a side quest here - it's the main storyline.
Learn more at UAT.edu.
Does UAT really have a campus cat?
Yes. Max is UAT's resident cat and a familiar part of campus life at the University of Advancing Technology in Tempe, Arizona.
What does "Senior Purrformance Analyst" mean?
It's a humorous nickname students use for Max because he frequently appears in project spaces and has a talent for showing up exactly when someone is trying to focus.
Can prospective students meet Max on a campus tour?
Often, yes - Max roams freely, and many tour groups do spot him. While he's not guaranteed (he's a cat, not a calendar invite), he's a common and memorable part of the tour experience.
What programs is UAT known for?
UAT is known for hands-on technology degree programs in fields such as, cybersecurity, AI, robotics, gaming, network engineering, and digital arts.
Curiosity isn’t a distraction here — it’s the engine. If you’re ready to build, break, and rethink the future of technology, start your journey at UAT. Learn more here.

Technology evolves faster than traditional degree paths can sometimes follow. The Technology Studies degree at the University of Advancing Technology (UAT), located in Tempe, offers a flexible, interdisciplinary approach that allows students to build a customized academic pathway aligned with their career goals.
Rather than focusing on a single discipline, Technology Studies empowers students to combine multiple areas of interest—such as cybersecurity, software development, digital marketing, game design, network engineering, or emerging technologies—into a cohesive, career-ready degree.
Today’s employers value professionals who understand how different technologies intersect. Innovation often happens at the crossroads of disciplines—where business meets data, where cybersecurity meets cloud infrastructure, or where digital media integrates with AI.
UAT’s Technology Studies program enables students to explore multiple technical domains while building a strong foundation in problem-solving, systems thinking, and technical communication. This adaptable structure supports students who want to:
This degree is ideal for forward-thinking students who want flexibility without sacrificing technical depth.
The Technology Studies degree allows students to design a program that reflects their unique strengths and career ambitions. With guidance from faculty advisors, students select coursework across various technology disciplines, creating a tailored educational experience.
This flexibility supports students who may be interested in tech entrepreneurship, innovation management, product development, technical consulting, or roles that require broad technical fluency. Instead of being limited to one niche, graduates develop a comprehensive understanding of how technologies integrate within organizations.
Like all programs at UAT, Technology Studies emphasizes project-based learning. Students apply their interdisciplinary knowledge to real-world challenges, building portfolios that demonstrate technical capability and strategic thinking.
Practical experience may include:
This applied learning model ensures graduates are prepared to adapt, communicate, and innovate in professional environments.
Because the degree is customizable, career pathways are broad and adaptable. Graduates pursue roles such as:
Arizona’s expanding technology ecosystem—especially throughout the Phoenix metropolitan area—offers opportunities in startups, enterprise organizations, cybersecurity firms, and digital media companies. Studying in Tempe positions students within a growing innovation corridor.
The Technology Studies degree builds versatile competencies that remain valuable as industries evolve. Students graduate with:
This foundation allows graduates to pivot as new technologies emerge, making the degree particularly valuable in fast-changing industries.
1. What is a Technology Studies degree?
It is an interdisciplinary technology program that allows students to customize coursework across multiple tech fields.
2. Who should consider this degree?
Students who want flexibility, interdisciplinary learning, or hybrid career pathways in technology.
3. Is this degree technical?
Yes. Students build technical competencies while integrating knowledge from multiple disciplines.
4. Can I specialize within Technology Studies?
Yes. Students work with advisors to shape a focused pathway aligned with career goals.
5. Is Arizona a good place to study technology?
Yes. Arizona’s growing technology and innovation sectors create expanding career opportunities.
Technology doesn’t fit into a single box—and neither should your education.
Apply now to the University of Advancing Technology or learn more about our flexible, technology-driven degree programs today.

University of Advancing Technology (UAT) in Tempe, Arizona, has officially launched a UAT Productions podcast "Tech Respect", a new technology-focused series hosted by Robert Walker, UAT Director of Community Initiatives.
The podcast is now streaming on YouTube, Spotify, and iHeartRadio.What Is the Tech Respect podcast?
Tech Respect is a technology podcast created by University of Advancing Technology to explore emerging trends, innovation, and career pathways in high-growth tech industries.
Each episode features conversations with:
The podcast reflects UAT’s hands-on, industry-aligned approach to technology education.

The podcast is hosted by Robert Walker, UAT’s Director of Community Initiatives. Walker leads in-depth discussions that highlight student innovation, industry insights, and the real-world application of advancing technologies.
His role at UAT centers around building community partnerships and elevating student engagement—making him uniquely positioned to connect academic innovation with industry trends.
Tech Respect is available on major streaming platforms, including:
The first two episodes are out now! Episode 3 is scheduled for publish on April 16, 2026.
Tech Respect explores high-demand technology fields and the people shaping them. Topics include:
In addition to industry trends, the podcast highlights the voices and achievements within the UAT community. Episodes feature:
By blending emerging technology discussions with faculty insight, student achievement, and alumni impact, Tech Respect offers a comprehensive look at the innovation ecosystem at University of Advancing Technology.
The launch of Tech respect extends the university’s commitment to innovation beyond the classroom. Based in Tempe, Arizona, UAT has built its reputation on project-based learning and industry-driven degree programs.
The podcast serves multiple purposes:
As the demand for skilled technology professionals continues to grow, Tech Respect positions the University as an active voice in conversations shaping the future of innovation.
Ready to move from listener to creator? Apply to UAT and start building emerging technology solutions.

This spring, the University of Advancing Technology (UAT) partnered with AZStRUT in the spirit of community and hands-on impact—refurbishing more than 55 computers for reuse across Arizona.
What might seem like a simple IT exercise quickly became something more meaningful. Students, staff, and volunteers worked side by side to bring devices back to life, ensuring each machine was ready for a second chapter.
The refurbishing process went beyond basic cleanup. Each computer was carefully inspected, cleaned, and restored to working condition. Teams tested essential components like cameras, microphones, and Wi-Fi connectivity, making sure every device met functional standards before being cleared for donation.
These efforts directly support access to technology in education. A portion of the refurbished devices—including Chromebooks—will be used at a middle school STEM fair, helping introduce younger students to hands-on learning experiences powered by accessible technology.
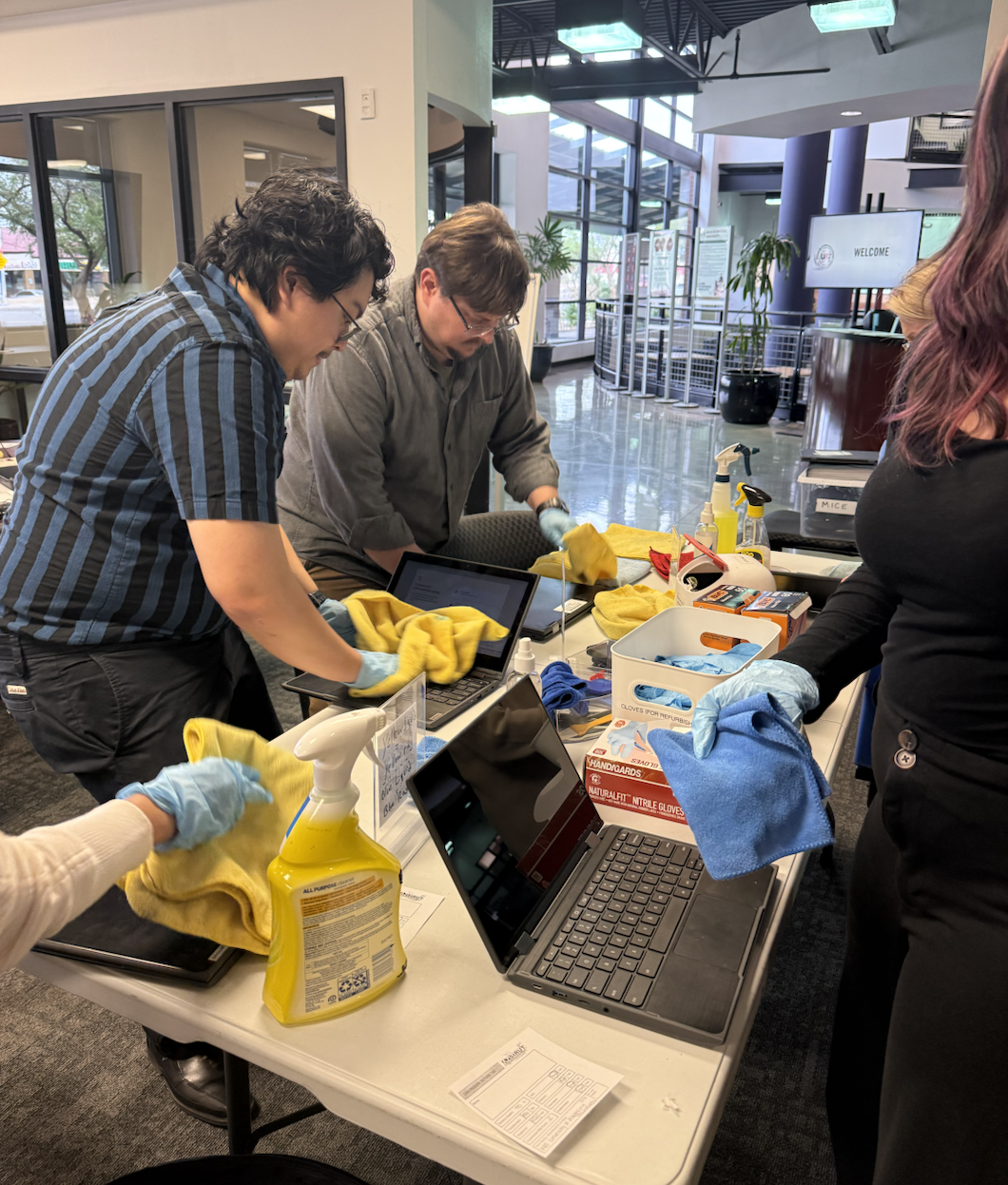
This initiative builds on a long-standing relationship between UAT and AZStRUT, a partnership that dates back to the early 2000s. Over the years, the collaboration has supported a wide range of efforts centered on technology reuse, digital equity, and community engagement.
More than just a refurbishing effort, this event reflects a shared commitment: extending the life of technology while expanding opportunity for others.
At UAT, innovation isn’t just about creating what’s next—it’s also about making sure more people have access to it.
Learn more about advancing technology degrees.

University of Advancing Technology (UAT) recently partnered with the Girl Scouts–Arizona Cactus-Pine Council to host a hands-on MakerFest, welcoming Girl Scouts to campus for a morning of creativity, exploration, and technical discovery.
The event introduced participants to the spirit of the maker movement—where curiosity, experimentation, and problem-solving come together to transform ideas into real-world creations. Throughout the morning, scouts engaged with UAT faculty and staff in a series of interactive experiences designed to demystify technology and encourage confidence in building and designing.
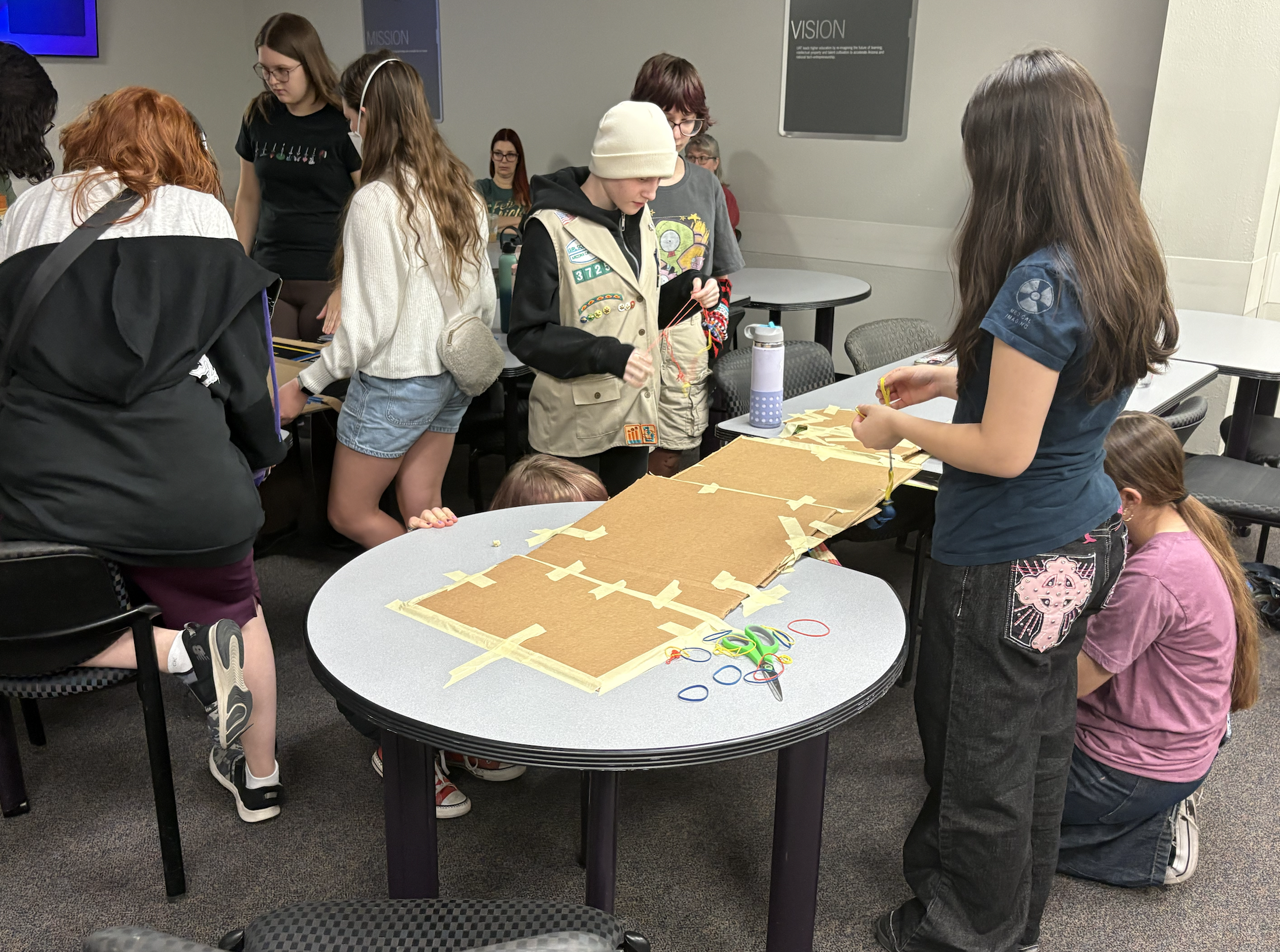
One of the highlights of the event took place in UAT’s Maker’s Lab, where participants were introduced to the fundamentals of digital fabrication and electronics. Guided by UAT Program Support Specialist, Tyler Widener, students explored how tools like 3D printers transform digital concepts into physical objects and learned basic soldering techniques used in electronics and hardware development. For many attendees, it was their first opportunity to see how engineering concepts translate into tangible projects.

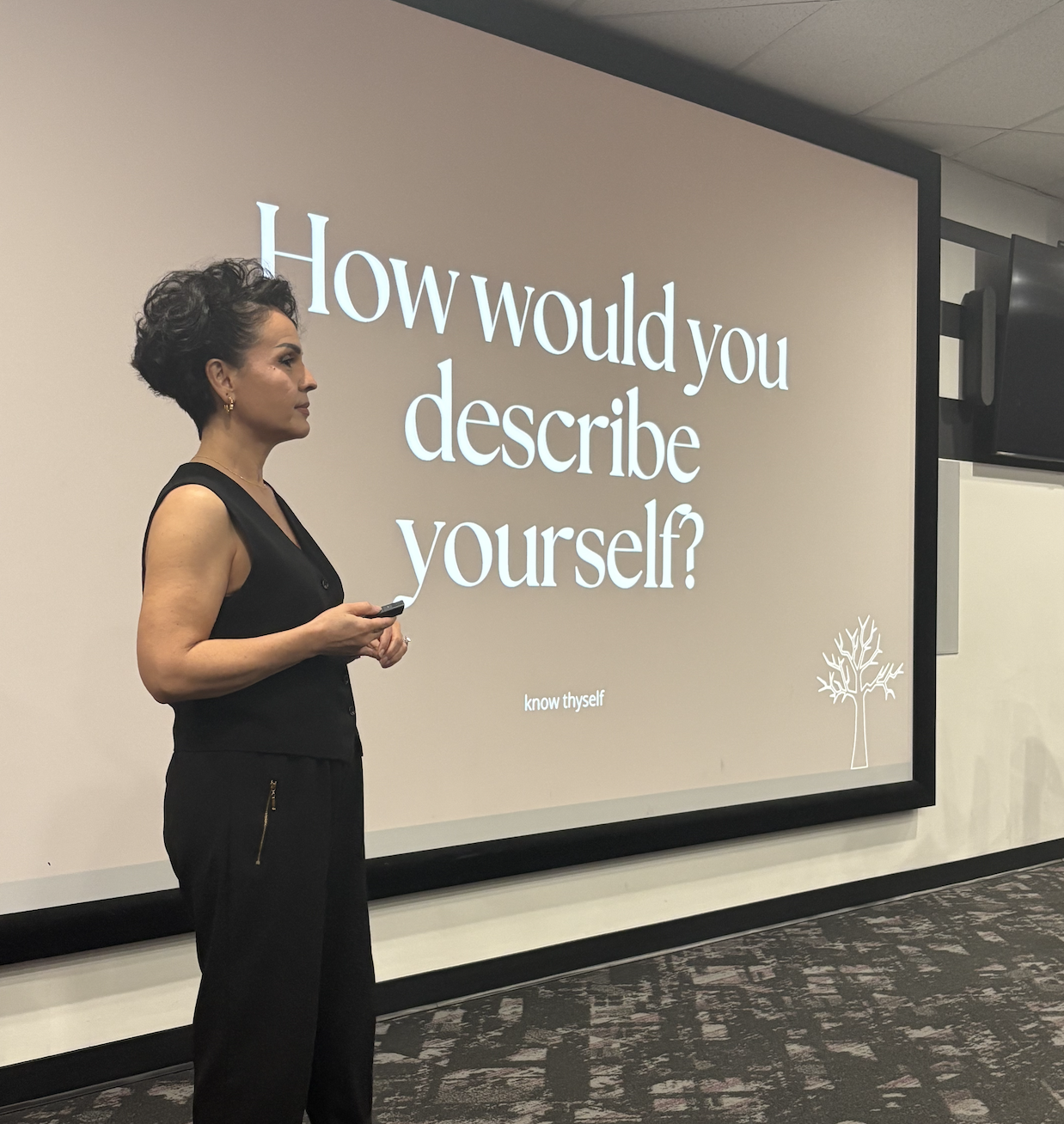
The event also emphasized that innovation extends beyond the act of building. During a session led by UAT Senior Professor, Dapzury Valenzuela, participants learned about the importance of storytelling, personal branding, and communicating the value of their ideas. By encouraging students to think about how creators present and share their work, the session connected technical skills with entrepreneurship and creativity.
The morning concluded with an opportunity for participants and their families to learn more about UAT’s approach to technology education and the pathways available to students interested in pursuing careers in STEM fields.
Events like MakerFest reflect UAT’s commitment to strengthening the technology pipeline by engaging young learners early and showing them that innovation is accessible to everyone. By partnering with organizations like the Girl Scouts, the university continues to create meaningful opportunities for students to explore technology in a welcoming and hands-on environment.
For the Girl Scouts who attended, the experience was more than a campus visit—it was a chance to see themselves as makers, problem-solvers, and future leaders in technology.

As technology becomes more embedded in everyday life, how people interact with digital systems matters more than ever. University of Advancing Technology (UAT) offers a Human Computer Interaction (HCI) degree focused on designing intuitive, accessible, and user-centered experiences. Based in Tempe, Arizona—and available Online/Hybrid—this degree prepares students to shape how users experience software, devices, and emerging technologies.
No matter how advanced a system is, it fails if people can’t use it effectively. Human Computer Interaction professionals ensure technology is intuitive, efficient, and human-centered. An HCI degree teaches students to design experiences that improve usability, satisfaction, and accessibility.
HCI blends cognitive psychology, design, and computer science principles. Students learn how users think, behave, and make decisions when interacting with technology—insight that is critical for building successful digital products.
Modern technology must serve diverse users across devices, abilities, and environments. UAT’s HCI program emphasizes inclusive design, usability testing, and ethical technology development, preparing graduates to create responsible and effective digital experiences.
UAT’s HCI degree combines research, design, and applied technology skills through hands-on projects.
CSC102 Introduction to Programming
Students graduate with portfolios demonstrating their ability to design, test, and improve user experiences across platforms.

This degree is ideal for students who are interested in UX, UI, and product design and enjoy improving how people interact with apps, websites, and digital tools. It’s well suited for analytical and creative thinkers who like combining research, problem-solving, and visual design to create intuitive user experiences. A Human Computer Interaction degree also appeals to technology advocates who care about accessibility, usability, and ethical design, and who want to make a meaningful impact through human-centered technology. With flexible learning options, UAT’s HCI degree is a strong fit for career changers and online learners looking to transition into UX- and design-focused technology roles.
A degree in Human Computer Interaction opens doors across tech, finance, healthcare, and entertainment. Your possible career outcomes are creative and high-demand:
UI/UX Designer: Create the look, feel, and flow of apps and websites.
Product Designer: Oversee the entire user journey of a digital product from concept to launch.
User Researcher: Conduct studies and interviews to uncover what users truly need.
Interaction Designer: Focus on the specific animations and responses when a user touches a screen.
Accessibility Specialist: Ensure digital products are usable by people with disabilities.
Frontend Developer: Bridge the gap by both designing the interface and writing the code to implement it.
UAT’s campus in Tempe, Arizona places students near a growing tech ecosystem in the Phoenix metro area, where the university’s technology-first approach encourages interdisciplinary collaboration with peers in Software Engineering, Game Design, and Digital Marketing. Through project-based learning and usability-focused coursework, students gain real-world experience and graduate with career-ready UX portfolios. UAT’s Human Computer Interaction degree prepares students to design technology that truly works for people, offering a future-focused pathway into user experience and interaction design careers for students in Arizona or online.

What is Human Computer Interaction as a field of study?
Human-Computer Interaction focuses on how people interact with technology and how systems can be designed to be more usable, accessible, and intuitive.
Is HCI more design-focused or technical?
HCI blends both. Students learn design principles, research methods, and technical concepts related to digital systems.
Do HCI students build a portfolio at UAT?
Yes. Portfolio development is central to the program, with projects involving research, prototyping, and usability testing.
Do I need a background in coding or design to enroll?
No prior experience is required. This degree is designed to build skills progressively for students from diverse backgrounds.
Is an HCI degree worth it in today’s job market?
Yes. As user experience becomes a key differentiator for digital products, demand for HCI and UX professionals continues to grow.
Ready to design the future?